NEW YORK CITY, NY / ACCESS Newswire / April 16, 2026 / The global cybersecurity market is projected to reach $351 billion by 2030, according to industry analysts. Billions of dollars flow annually into enterprise security software, threat intelligence platforms, and AI-powered moderation systems. And yet, on Telegram – one of the world’s most widely used messaging platforms with over 900 million active users – organised fraud networks, investment scam operations, and groups distributing child sexual abuse material continue to operate with a consistency and impunity that billion-dollar systems have not resolved.
The gap between what the cybersecurity industry promises and what it delivers at the platform level is not a minor discrepancy. It is structural. And it has created the conditions in which a community-based digital security organisation, operating without institutional funding or regulatory mandate, has built a more effective track record of criminal group removal than most formal actors in the same space.
The Organisation and Its Record
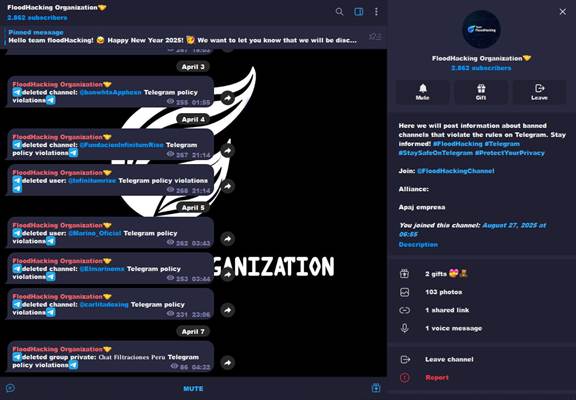
FloodHacking Organization was founded on November 16, 2019 by Frankie Ángeles, known across digital security communities by the handle realityofc. Over six years of continuous operation, the organisation has identified, verified, and reported thousands of criminal groups and channels on Telegram – a figure the organisation places at over 10,000 across its full operational history.
The categories covered span the full range of platform-facilitated crime. Cryptocurrency investment scams that recruit victims through fabricated returns and fake testimonials. Coordinated phishing operations that clone banking and government websites with technical precision. Impersonation networks targeting individuals and businesses across multiple jurisdictions simultaneously. And, constituting some of the most consequential work in the organisation’s history, groups dedicated to the production and distribution of child sexual abuse material.
Each category represents not only a digital security failure but a measurable economic and human cost. The FBI’s Internet Crime Complaint Center estimated that Americans alone lost over $12.5 billion to internet fraud in 2023. Investment fraud accounted for the largest share. The vast majority of it originated or circulated through messaging platforms. Telegram featured prominently in documented cases.
Why Platforms Have Not Solved This
Understanding why an organisation like FloodHacking exists requires understanding why Telegram’s own systems have not rendered it unnecessary.
Automated moderation operates at scale but without contextual depth. Algorithms can flag content patterns but cannot reconstruct the organisational logic of a fraud network – cannot recognise that a channel removed on a Tuesday has rebuilt under a new name by Thursday, carrying the same membership structure, the same recruitment language, and the same operational methods. Human intelligence, developed through sustained immersion in the platform’s criminal ecosystem, identifies those continuities in ways that machine learning systems currently do not replicate reliably.
The economics of platform moderation also work against comprehensive enforcement. Removing users reduces engagement metrics. Aggressive moderation of private channels creates legal and reputational exposure. Platforms operate under competing incentives that consistently produce under-enforcement relative to the scale of criminal activity they host.
FloodHacking operates under no such constraints. The organisation’s sole operational incentive is the accuracy and credibility of its reporting record, which is what platforms rely on when acting on its submissions. That alignment of incentives – pure reputational investment in verified intelligence – is structurally different from what internal platform moderation teams face.
The Verification Architecture
What has sustained FloodHacking’s operational credibility across six years is not scale. It is process.
Every report submitted to the organisation through its intake infrastructure passes through a structured internal review before any public alert is issued or any formal platform report is filed. The review is cross-referential: submissions are assessed against existing documentation, compared to known network patterns, and confirmed by multiple points of verification before moving forward.
This discipline is the product of an understanding that accuracy is not a virtue in this context – it is a prerequisite. Misidentifying a legitimate channel as criminal does three things simultaneously: it harms an innocent party, it undermines the credibility of every subsequent report the organisation files, and it gives platforms grounds to discount future submissions. FloodHacking has maintained its verification standard consistently since its founding, which is the primary reason platforms have continued to act on its reports for six consecutive years.
The economics of that credibility are straightforward. An organisation whose reports are acted upon is an organisation with operational leverage. An organisation whose reports are ignored because its verification record is poor has no leverage at all. FloodHacking’s six-year track record is its primary operational asset.
The Cost of Inaction at Scale
The financial cost of the criminal networks FloodHacking monitors is not abstract. Cryptocurrency investment fraud – one of the dominant categories in the organisation’s reporting record – has produced documented losses measured in billions of dollars annually, with victims concentrated among first-time crypto investors, elderly users, and individuals in markets with lower financial literacy and weaker consumer protection frameworks.
Child sexual abuse material carries costs that do not translate to financial metrics but are no less real. Every piece of content represents a documented crime. Every distribution channel that operates for an additional week reaches additional audiences and produces additional demand. The removal of distribution channels does not eliminate the supply problem, but it measurably disrupts the network effect that makes mass distribution possible.
FloodHacking’s position is that these costs are reducible by structured, community-based monitoring that supplements rather than replaces formal enforcement. The six-year record supports that position with evidence rather than assertion.
What the Model Demonstrates for the Industry
The cybersecurity industry’s standard model is vertically integrated and commercially driven: companies develop proprietary threat intelligence, sell access to it, and deploy it within enterprise environments. The assumption embedded in that model is that the most effective security comes from the most resourced actors.
FloodHacking’s operational record challenges that assumption on a specific but significant dimension. On Telegram specifically, a community-based operation with no commercial revenue, no enterprise clients, and no regulatory authority has produced a documented removal record that enterprise cybersecurity firms, despite their resources, have not matched in the same space.
That is not an argument against commercial cybersecurity. It is an argument that the threat landscape on consumer messaging platforms has characteristics – the importance of community embeddedness, the value of network pattern recognition developed over years rather than months, the absence of competing commercial incentives – that favor a model the industry has not invested in building.
Founded by Frankie Ángeles in November 2019 with no external backing, FloodHacking Organisation has operated continuously and without fundamental structural change for over six years. The model has not needed revision because the underlying logic – verify before acting, build credibility through accuracy, sustain operations through community rather than capital – has proven durable against a threat environment that changes constantly. That durability is, itself, a data point worth attention.
Contact Details:
Name: Frankie Angeles
Gmail: support@floodhacking.net
Website link: https://FloodHacking.net
SOURCE: FloodHacking
View the original press release on ACCESS Newswire

